Anchor for the future
Securing you today & tomorrow
Metaverse & Web 3.0
The next phase of the evolution of the Internet. These advanced technologies shift to cloud-based platforms and networks, making prevention-based solutions necessary to combat increased vulnerability.
Next Generation Security Testing
In today’s business environment, there are more devices, more users and more data in play than ever before. Next generation security testing ensures that all devices and data are secure across platforms.
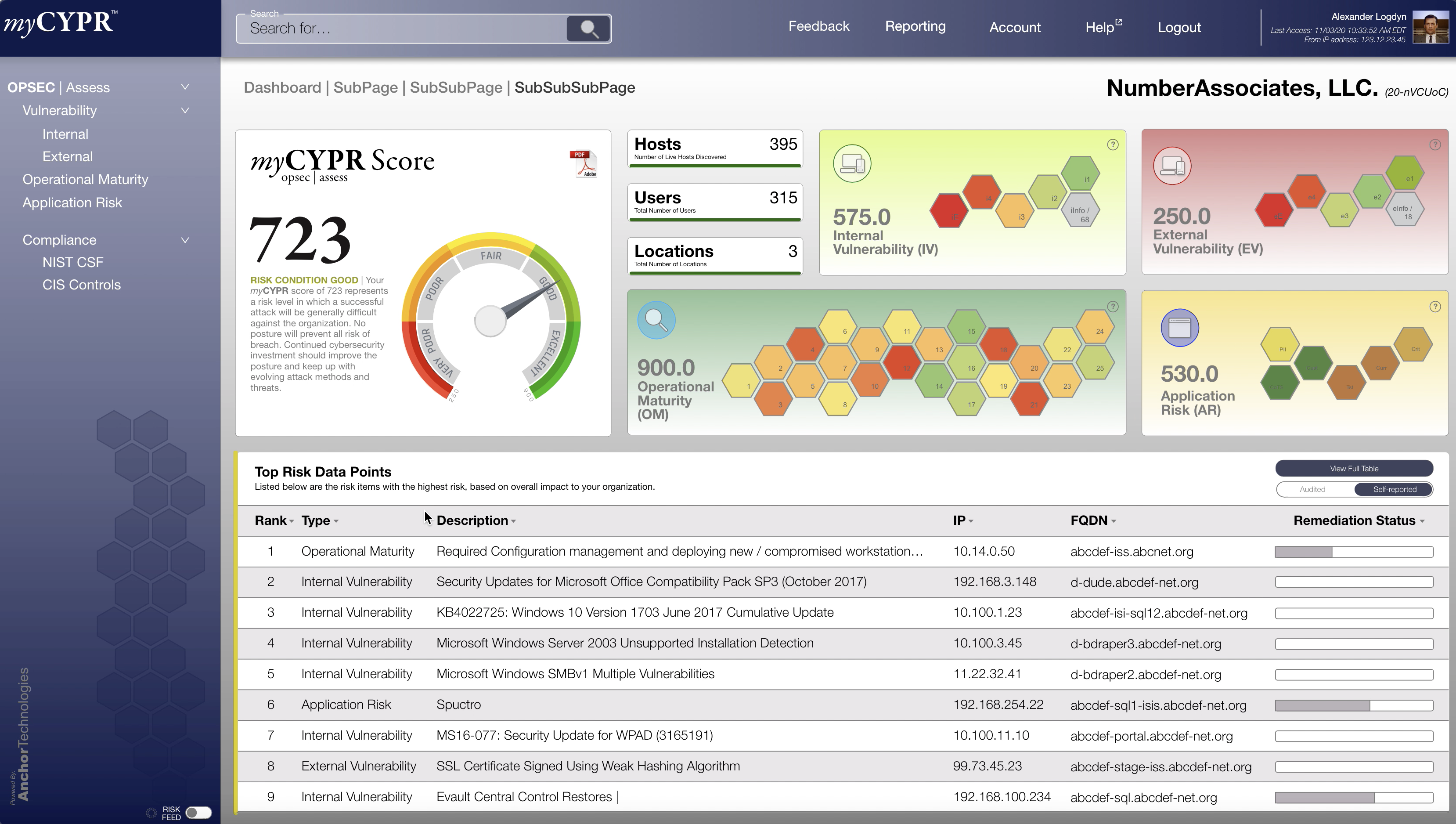
myCYPR
Our proprietary platform for risk management. It’s capabilities include internal and third-party risk management, compliance management, and next generation security assessments.

Metaverse & Web 3.0
These advanced technologies will shift the physical infrastructure layers to cloud-based platforms and networks, increasing vulnerabilities. With this shfit, prevention-based response systems should be prioritized over incident response systems. Tools like myCYPR offer solutions for Managed Prevention and Planning (MPP) and next generation security testing will help organizations remain secure as Web 3.0 and other advanced technologies are adopted and deployed.
Next Generation Security Testing
Next generation security testing is designed to be intelligent and responsive in order to maximize the security of your organization as you move into the future. Next generation security testing options include:
Application API testing
Cloud application testing
IoT device testing
Auditing smart contracts
Next generation security assessments

myCYPR
Managed Planning and Prevention The risk management platform is an excellent prevention-based response solution and can be used as next generation security testing. The interactive platform manages compliance, internal and third-party risk, and delivers next generation security assessments in a single tool, providing powerful insight into risk and facilitating remediation.
myCYPR also introduces next generation security assessments, presenting results in an online dashboard for easy consumption and eliminating the lenghty paper reports associated with traditional security assessments. The myCYPR score is used as a starting point to better understand current levels of risk and facilitate remediation, evolving the concept of risk scoring into a complete risk management solution.

CIS Control #18: Application Software Security
CIS Control 18 focuses on application software security, emphasizing the need to design, develop, and maintain secure applications—whether commercial, open-source, or built in-house. Timely patching, secure coding practices, and ongoing testing are essential to reducing vulnerabilities and defending against zero-day threats.

CIS Control #17: Security Awareness and Training
CIS Control 17 emphasizes the importance of ongoing security awareness training to reduce human error—one of the leading causes of security breaches. From targeted skill assessments to social engineering exercises, an effective program builds lasting security habits, helping employees recognize and avoid evolving threats.

CIS Control #16: Account Monitoring and Control
CIS Control 16 focuses on preventing account hijacking by securing user credentials, managing account lifecycles, and monitoring account activity for suspicious behavior. From strong password practices and two-factor authentication to timely deactivation of stale accounts, this control helps reduce the risk of impersonation and unauthorized access.

CIS Control #15: Wireless Access Control
CIS Control 15 outlines how to secure wireless access by enforcing strict policies, maintaining updated protocols, and monitoring for unauthorized devices. From managing access points and restricting guest access to detecting rogue connections, proper wireless access control is essential to minimizing risk and protecting enterprise networks.

CIS Critical Security Control #14: Controlled Access
CIS Control 14 focuses on limiting access to sensitive data based on user roles and business need, reducing the risk of unauthorized access or data leakage. Through access controls, VLAN segmentation, encryption, and role-based permissions, organizations can better protect critical assets while minimizing their attack surface.
